Security & Resiliency
Robust cybersecurity is essential to your future as a business. We put the security in your operations by delivering solutions that are purpose-built to secure your mission, without breaking your budget.
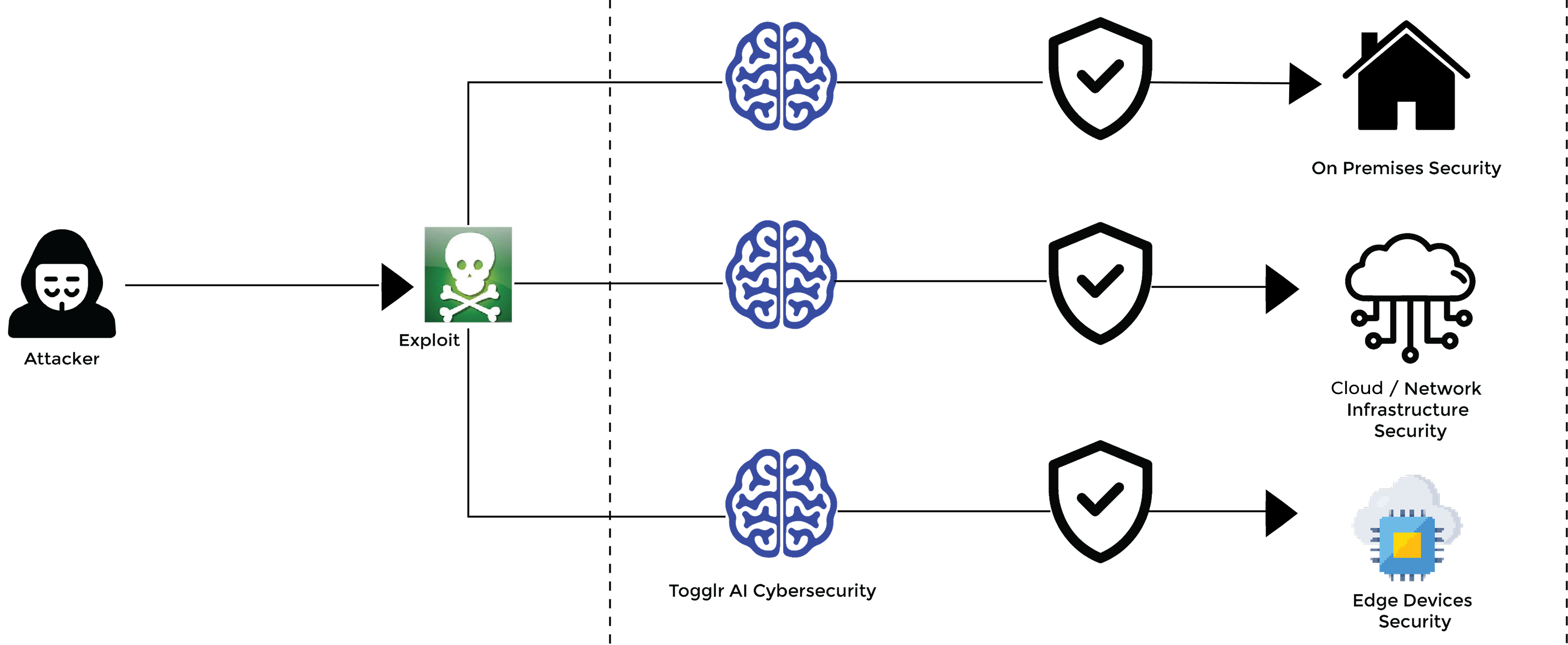
In today’s landscape, businesses prioritize mitigating risks, enhancing trust, and securing digital operations to achieve their goals while minimizing cybersecurity disruptions. Togglr empowers organizations to navigate cyber risks confidently, bolstering operational resilience and meeting regulatory requirements through an integrated security focus, strong cyber resilience expertise, and deep knowledge of compliance needs. Our Security and Resilience Services include advanced threat protection, cloud security solutions, and virtual machine backup capabilities.
We help businesses anticipate, protect, withstand, and recover from adverse conditions, attacks, and cyber compromises. Our consult-led approach and co-created solutions with customers and partners address unique cyber challenges quickly and effectively, maximizing security investment value. As one of the trusted cloud computing companies, we align our services with operational needs to ensure minimal disruption.
We offer advanced Deepfake Detection through Togglr, helping organizations combat misinformation, fraud, and security threats. Our AI-driven tool ensures real-time analysis, cross-format compatibility, and transparent authentication to safeguard digital content and brand trust.
Our experts assist in assessing and benchmarking cybersecurity maturity, defining target states, and ensuring visibility into threats. By applying consistent security policies and controls, we help both new and existing customers safeguard mission-critical data and systems. With a strong grasp of digital transformation risks and a broad technology platform range, we provide decades of refined methodologies to combat even the most complex cyber threats and disasters. These Security and Resilience Services are delivered with proven expertise.
Consulting
Consulting
Togglr provides cybersecurity consulting and advisory services company. With a strong focus on protecting businesses from digital threats, we offer expert guidance and innovative solutions to safeguard your organization’s sensitive data and digital assets
We bring together a team of industry-leading experts who stay at the forefront of technology and cybersecurity trends. Our commitment to continuous learning and innovation ensures that you receive the most advanced solution. Our dedicated team helps businesses navigate the complex landscape of cloud security regulations and standards, ensuring data protection and compliance. With Togglr, you can confidently embrace cloud technologies while safeguarding your assets from cyber risks.
We offer solutions to meet evolving regulatory requirements while securing your cloud infrastructure. Our experts ensure your data
is protected, and compliance is maintained, giving you peace of mind in an ever-changing digital landscape. We also specializes in providing comprehensive security audits and one-time services to safeguard your digital assets.
Our Offerings
- Audit Readiness Assessment
- Security Policy Assessment
- Cyber Security & Risk Consulting
- Policy & Compliance Consulting
- Incident Response
- Data Protection & Privacy Services
- Email Phishing advisory Services
Managed SOC Services
Managed SOC Services
Togglr offers flexible, modular Security Operations and Response Services designed to modernize security operations. Leveraging AI and automation, our end-to-end services enhance threat resilience, helping businesses anticipate, protect, and recover from cyberattacks. Togglr’s Security Operations Center (SOC) supports the entire threat lifecycle with integrated automation, enabling businesses to either collaborate with Togglr’s experts or fully outsource their security management. Our SOC provides tailored, compliant solutions across regions, ensuring data is processed locally to meet regulatory needs, while expert teams deliver rapid incident response and robust threat protection
- Fulfill their requirements using their current security toolset, teams, and meet them on their journey to modernize cyber operations.
- Automate security functions that are continuously updated to meet changing needs.
- Use flexible solutions for staffing, standard offerings, and use of cyber operations capabilities
Get centralized security management and integrated threat detection and response, combining SIEM, SOAR, VM, EDR and cloud security capabilities. Our dedicated team offers 24/7 vigilance to monitor, detect, and respond to security threats, ensuring robust protection for your digital assets. We prioritize your organization’s safety, delivering peace of mind in an ever-evolving threat landscape.
Our Offerings
- Threat Intelligent Service
- DDOS Mitigation Service
- MDR
- Managed EDR
- Managed Threat Hunting
- Managed SEIM
- Vulnerability Management Service
- Patch Management Services
- Incident Response and Forensic
- Security Operations as a platform
Incident Recovery Services
Incident Recovery Services
Targeted cyberattacks against data centres and cloud infrastructures are growing in complexity and sophistication.
Disruptions are inevitable. Digital transformation and cloud adoption are leading to an increase in attack surface. Threat actors are becoming stealthier, and regulatory compliance requirements are growing more complex.
Minimize the business impact of outages with fast, reliable, and scalable disaster and cyber recovery services across hybrid multicloud environments. Traditional disaster recovery planning and strategies are unable to keep up with changing cyber recovery requirements and may result in businesses being exposed to risks of outages that cause irreparable damage.
1. Incident Recovery Services from Togglr use best practices, purpose-built technologies, and expertise to assess your incident response readiness and build an incident recovery plan aligned to your business needs. help mitigate the impact of an outage and provide fast, reliable, and scalable recovery across hybrid multicloud environments.
2. As cybersecurity gaps continues to widen, business needs partner with deep expertise to help them assess cyber risk and establish policies , controls and compliances programs, that are closely aligned to business objectives. our offerings can mitigate the impact of an outage and provide fast, reliable, and scalable recovery across hybrid platform solutions.
Our Offerings
- Cyber Incident Recovery
- Managed Backup Services.
- Hybrid Platform Recovery
- Disaster Recovery as a Services
- ( AWS, GCP, MS, IBM)
Zero Trust Services
Zero Trust Services
The cybersecurity landscape has significantly expanded with evolving IT environments, workload and workforce distribution, cloud and digital adoption and consequent regulatory mandates.
Although organizations have invested in layered, in-depth security point solutions, the siloed approach makes it difficult to grapple with the growing sophistication and frequency of cyberattacks. Security leaders need to shift from the current siloed security approach to a new zero trust architecture—an integrated framework that is underpinned by governance across all five elements–identity, device, network, apps, and data.
Zero Trust Services from Togglr integrates multiple visibility points, automates detection and response, and performs risk-aware access decisions to ensure protection of critical applications, data, and systems and reduction of attack surface. Operating in a phased approach, Togglr Zero Trust helps secure what is most important based on your business needs, selects the right use cases and leverages public frameworks.
Our Offerings
- Identity
- Endpoint Security Services
- Data Protection and Privacy
- Privileged access management design and implementation
- Network and Edge Security Services
- Analytics Orchestration and Automation
- Access Management
- Application and Workload Security

